Static Analysis - Kamasers Malware
- sandeep karnik
- Nov 5, 2025
- 7 min read
Updated: Nov 23, 2025

This is a series of articles where we analyze Kamasers family of malware.
In this article we are starting off with static analysis. The malware sample is used from Malware Bazaar, located here:
Checking the file type
Using "file"

Using xxd
Shows the Windows Executable marker

Using ExeInfo
32 bit exe
Created using MS Visual C++
Not packed

Finding SHA-256
┌──(kali㉿kali)-[~/ma-samples/kamasers]
└─$ shasum -a 256 malware.exe.infected
12d5e3fdac938bef0d9c78e7905d6d1deaca21602aaef3fdc900b0063edb40f9
VirusTotal Scan
Scanned the SHA-256 hash at VirusTotal. Quite a few security vendors have flagged it as Trojan, Dropper.

Analyzing strings
Let's use "strings" and "floss" utilities to identify different strings in the malware. Listing here only those that stand out.
Strings that denote imported functions
CreateDirectoryW
GetModuleFileNameA
:
:
CreateFileW
HeapSize
WriteConsoleW
SetEndOfFileThis import set strongly suggests a Windows C/C++ loader with these likely capabilities:
Built with MSVC C++ runtime (STL, exceptions, i/o).
Uses Resource APIs to load embedded data.
Uses CryptoAPI to derive/decrypt data (payload/config).
Performs process injection / hollowing (suspend, write memory, set context, resume).
Uses COM (CoInitializeEx / CoCreateInstance) for some tasks (WMI, Task Scheduler, MSXML, BITS, Shell, etc.).
Uses file APIs and Known Folder calls to stage or copy files.
Uses mutex for single instance.
Uses SEH / IsDebuggerPresent and other basic anti-analysis checks.
Handles Unicode/locale conversions carefully (MultiByteToWideChar, LCMapString*, etc.).
Multi-threaded primitives (CriticalSection, TLS/FLS) are present.
This malware is possibly a resource-based loader that:
Reads an encrypted blob from PE resources,
Uses CryptoAPI to derive/decrypt the blob,
Spins up a benign-looking child process in CREATE_SUSPENDED mode,
Injects the decrypted payload into that process (WriteProcessMemory / SetThreadContext),
Resumes the thread (ResumeThread) to execute the payload (classic RunPE / process hollowing).
COM calls may be used for staging or to interact with platform services. Networking or persistence may be performed by the injected second stage rather than the initial stub.
Looks like some keys / urls etc. are generated dynamically from this character set. Generally done to create passwords / api secrets / URLs etc.
abcdefghijklmnopqrstuvwxyz
ABCDEFGHIJKLMNOPQRSTUVWXYZOoh! Someone forgot to sanitize the exe
C:\Users\4674\Desktop\04-10-2025CrypterFramework\CrypterFramework\CrypterFramework_v3\Release\LoaderStub.pdbLots of country names, language locales are found using floss. May suggest multilingual support.
canadian
chinese
chinese-hongkong
chinese-simplified
dutch-belgian
english-american
english-aus
english-belize
english-can
:
:
:
eu-ES
mk-MK
tn-ZA
xh-ZA
zu-ZA
af-ZA
ka-GEStrings that may indicate files opened/created
Microsoft Corporation
LogonTrigger
\SystemSync
\svchost.exe
"LogonTrigger"
This is a term used by the Windows Task Scheduler XML schema. It indicates a scheduled-task trigger that runs at user logon.
If present in the binary strings, the sample may either:
contain a scheduled-task XML template it will register, or
reference Task Scheduler APIs / COM interfaces to create a task with a Logon trigger.
For later reference: Look for related imports: `taskschd.dll`, `schtasks.exe` usage, or Task Scheduler COM CLSIDs.
"\SystemSync"
Look for file opened with this name
"\svchost.exe"
Likely a command-line or spawn target. Two common interpretations:
The sample may attempt to create or masquerade as `svchost.exe` (dropper places a copy named svchost.exe).
The sample may schedule or launch `svchost.exe` as a legitimate host to run code (more often used as target for process-hollowing / injection).
If seen together with LogonTrigger + \SystemSync, it suggests the sample might create a scheduled task named `\SystemSync` that runs `svchost.exe` (possibly with arguments), or it creates/injects into `svchost.exe`.
Threats Revealed by now
High suspicion pattern:
Binary contains Task Scheduler XML/name + “LogonTrigger” + system-looking task name + svchost.exe → likely persistence via scheduled task that either:
launches a benign executable which gets hollowed/injected, or
launches a dropped binary named like `svchost.exe` to blend in.
Decoded Strings
NtUnmapViewOfSection
NtUnmapViewOfSection
Native API often used in PROCESS HOLLOWING / RunPE.
Typical sequence:
CreateProcess*(CREATE_SUSPENDED) ->
NtUnmapViewOfSection(remote, base) ->
VirtualAllocEx ->
WriteProcessMemory ->
SetThreadContext/ResumeThread.
Confirms a more “aggressive” hollowing variant that unmaps the target’s image before writing the new one.
Analyzing Import Table



Malware Import Summary
Process & Thread Manipulation - CreateProcessA/W, WriteProcessMemory, VirtualAllocEx, SetThreadContext
Suggests process hollowing or code injection
Cryptography API Usage - CryptAcquireContextW, CryptEncrypt, CryptDecrypt, CryptHashData
Indicates payload/config encryption or secure comms
Resource & Memory Handling - LoadResource, FindResourceA, LockResource, SizeofResource, VirtualAlloc
Implies embedded encrypted payload unpacked in memory
Anti-Debugging & Evasion - IsDebuggerPresent, QueryPerformanceCounter, RaiseException
Used for debugger/sandbox detection or timing checks
Mutex & Synchronization - CreateMutexA
Ensures single instance execution on host
System & Environment Queries - GetCommandLineA/W, GetModuleFileNameW, GetSystemTimeAsFileTime
Gathers system metadata for C2 or evasion logic
File & Console Operations - ReadFile, WriteFile, CreateDirectoryW, ShowWindow
Basic file I/O or console control for dropper behavior
[+] Overall Assessment:
Likely a loader or stage-1 dropper that:
- Decrypts and injects payload into a legitimate process
- Uses CryptoAPI for encryption/decryption
- Employs anti-debug and mutex for evasion & stability
- Operates filelessly by unpacking payload from resources
Inspecting PE Sections

.rsrc section has very high entropy suggesting compressed or encrypted data
Unusual section "fptable"
Entry Point is not marked to be in any of the section. If it was packed, there would have been the bootstrap section that would unpack it.
Raw sizes and virtual sizes almost match - again, not packed.
The .reloc section in a Windows PE file stores the Base Relocation Table, which helps the Windows loader adjust absolute memory addresses if the executable isn’t loaded at its preferred base address. Normally, this section is small, structured, and low in entropy, containing relocation entries like address offsets and types (e.g., IMAGE_REL_BASED_DIR64).
In this sample, however, the .reloc section shows an unusually high entropy (≈6.5) and larger-than-expected size, indicating it likely doesn’t contain standard relocation data. This suggests the malware author repurposed the section to hide encrypted or compressed payload data, a common evasion technique seen in packed or multi-stage malware.
Let's extract the blob in .rsrc section and analyze it further.
I wrote a small python script to do this extract.
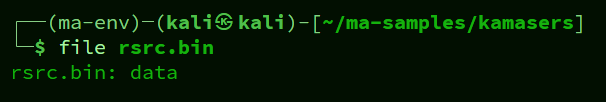
┌──(ma-env)─(kali㉿kali)-[~/ma-samples/kamasers]
└─$ cat extract-rsrc.py
import pefile, sys
pe = pefile.PE("malware.exe.infected")
sec = next((s for s in pe.sections if s.Name.rstrip(b'\x00').decode(errors='ignore')=='.rsrc'), None)
if sec is None:
print("No .rsrc section found.")
else:
data = sec.get_data()
with open("rsrc.bin","wb") as f:
f.write(data)
print("Wrote rsrc.bin, size", len(data))
Running strings on rsrc.bin shows these interesting strings (other noise ignored)
PA<?xml version='1.0' encoding='UTF-8' standalone='yes'?>
<assembly xmlns='urn:schemas-microsoft-com:asm.v1' manifestVersion='1.0'>
<trustInfo xmlns="urn:schemas-microsoft-com:asm.v3">
<security>
<requestedPrivileges>
<requestedExecutionLevel level='asInvoker' uiAccess='false' />
</requestedPrivileges>
</security>
</trustInfo>
</assembly>
PADPADDINGXXPADDINGPADDINGXXPADDINGPADDINGXXPADDINGPADDINGXXPADDINGPADDINGXXPADDINGPADDINGXXPADDINGPADDINGXXPADDINGPADDINGXXPADDINGPADDINGXXPAD
What might this mean:
<?xml version='1.0' ...</assembly> — an application/assembly manifest. Many Windows executables include an embedded manifest (declares requested execution level, WinSxS assembly info, etc.). Finding it inside rsrc.bin strongly suggests the resource blob contains a normal app manifest (likely stored under RT_MANIFEST).
The repeating PAD / PADDING text (PADPADDINGXXPADDING...) is almost certainly filler/padding placed by whoever created the resource or packer. That literal ASCII padding is used to:
align resource blocks to boundaries, or
mark unused space, or
be replaced later (placeholder).
Nothing in that snippet looks like a compressed PE or obvious encrypted blob by itself — it looks like plain ASCII XML + explicit padding.
Let's try to visualize how the padding is used around the human readable words.
Just for fun, let's see how a block of bytes around the first one looks. Let's first see the hex offsets of where some of the human readable word are found:

What's next to 0x6b22d:

While that's all fine, we don't have the actual payload that's embedded in all this noise, and part of the .rsrc section. Let's use Resource Hacker tool to extract the exact payload.

Saving this to a file. Seems like an encrypted blob. Couldn't see any meaningful string extracted using floss.
However, this points towards the direction that payload is embedded in .rsrc section.
Also extracted .reloc section to a binary file - the file type is "Data" as above, but no interesting human readable string found.
Other PE headers
Compiled pretty recently, on 31st Oct 2025

YARA Rules
We can create a few yara rules based upon the information that we have
Rule based upon the PDB path:
rule Kamasers_LoaderStub_PDB
{
meta:
author = "palavi.tech"
date = "2025-11-07"
strings:
// full original path (ASCII, case-insensitive)
$pdb_full_ascii = "C:\\Users\\4674\\Desktop\\04-10-2025CrypterFramework\\CrypterFramework\\CrypterFramework_v3\\Release\\LoaderStub.pdb" ascii nocase
// filename-only (useful when path is stripped)
$pdb_name = "LoaderStub.pdb" ascii nocase
// wide/UTF-16-LE versions (common in PE resources, memory dumps)
$pdb_full_wide = "C:\\Users\\4674\\Desktop\\04-10-2025CrypterFramework\\CrypterFramework\\CrypterFramework_v3\\Release\\LoaderStub.pdb" wide nocase
$pdb_name_wide = "LoaderStub.pdb" wide nocase
condition:
any of ($pdb*)
}
And the other one based upon the rsrc payload:
rule Kamasers_EncryptedPayload_Rsrc
{
meta:
author = "palavi.tech"
date = "2025-11-07"
strings:
/* 24-byte sequence chosen from the start of the displayed blob */
$seq1 = { 6F 77 2D E3 06 60 AA F9 F8 40 B2 26 1A 54 86 90 87 C1 82 AF 9E EF 95 79 A2 }
/* shorter 12-byte fallback (in case the longer sequence is altered/truncated) */
$seq2 = { 6F 77 2D E3 06 60 AA F9 F8 40 B2 26 }
condition:
any of ($seq*) and filesize < 20MB
}
Summarizing the findings we have till now
Sample is malicious Kamasers-family Windows malware: SHA-256 12d5e3fdac938bef0d9c78e7905d6d1deaca21602aaef3fdc900b0063edb40f9 and multiple VirusTotal vendor detections.
Loader reads and executes an encrypted secondary payload from PE resources: presence of resource-related imports/strings (e.g., FindResourceA, SizeofResource) combined with large non-text resource-like artifacts implied by analysis and no obvious plaintext payload.
Uses CryptoAPI-style decryption/derivation for the embedded blob: crypto-related imports/strings and decryption/derivation patterns observed in the static output.
Performs aggressive process hollowing / RunPE behavior to execute the payload stealthily: typical sequence functions/strings present: CreateProcess*(CREATE_SUSPENDED), NtUnmapViewOfSection, VirtualAllocEx, WriteProcessMemory, SetThreadContext, ResumeThread.
Likely persists via Task Scheduler or registers a Logon trigger task named like \SystemSync: strings LogonTrigger, \SystemSync, and references to scheduler/COM APIs suggest creating a scheduled task for persistence.
May use or masquerade as svchost.exe as a spawn/hollowing target or dropped filename to blend in: presence of \svchost.exe string alongside scheduled-task indicators.
Built with MSVC C/C++ runtime and uses standard CRT/STL features: imports and usage patterns (C++ runtime symbols, i/o, exceptions found from strings output) indicate an MSVC C/C++ build.
Contains multi-language/locale artifacts suggesting multi-region messaging or config generation: many locale/country strings found (e.g., chinese, english-american, eu-ES, af-ZA, etc.).
Uses mutex and threading / synchronization primitives and basic anti-analysis checks: imports/strings for mutex usage, CriticalSection/TLS primitives, and checks like IsDebuggerPresent/SEH references.
Not heavily packed/obfuscated at the outer layer (loader stub is plain enough) — PDB path leaked (LoaderStub.pdb pointing to CrypterFramework build) and readable strings reduce evidence of a full packer.
Decoded/native API usage confirms low-level unmapping for hollowing — explicit mention of NtUnmapViewOfSection corroborates unmap-then-map hollowing variants.
Next technical steps are clear: dynamic execution in a controlled lab, extract & decrypt resource blob, monitor injection/persistence/network I/O, and create detection rules: this follows from the static indicators above (resource+crypto+injection+persistence strings and VT detections).
END OF PART 1
Got a suspicious file or malware sample you'd like us to dissect? PalaviTech's analysts can reverse-engineer it for you - Visit https://palavi.tech/malware-analysis to get started



Comments